Blind Men and the Elephant: the story of cybersecurity
Our view of cybersecurity is defined by our backgrounds, and that perspective is usually very limiting
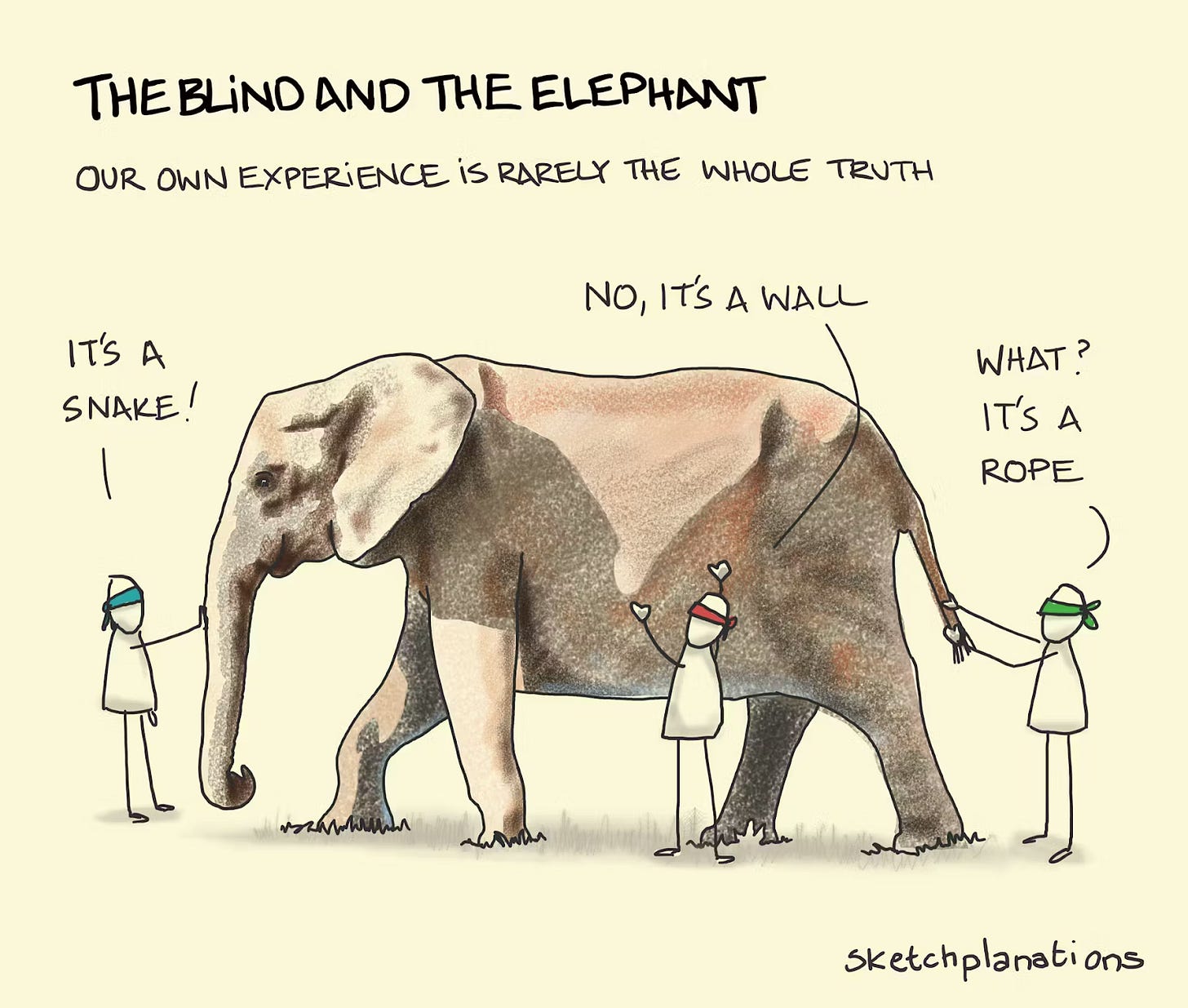
Blind men and the elephant
There’s an old story about a group of blind people who come across an elephant for the first time. Since they can’t see it, each of them tries to understand what it is by touching a different part. One person grabs the trunk and says the elephant is like a snake, another feels a leg and says it’s like a tree, a third touches the ear and thinks it’s like a big fan, and someone else holds the tail and says it’s like a rope. Each of them is sure they are right, because what they feel is real to them, and they definitely are, even if they don’t fully realize that each of them only has one part of the story. I’ve seen different versions of this story; in some, people start arguing and fighting over who is right, and in others, they work together to complement each other’s learning and perspectives.
This issue is brought to you by... Island.
Say Yes to AI—Without Leaking Your Data
Employees are already using AI tools, whether you’ve approved them or not. The real risk isn’t AI itself. It’s sensitive data slipping into prompts with zero visibility or control.
Island AI Protect secures AI at the point of use: the browser. It monitors every prompt and response in real time, blocking or redacting sensitive data while giving security and IT teams full visibility into AI usage.
No bans. No friction. Just safe, governed AI adoption.
I am sure you already understand where I am going with this, and if you do, you are probably almost right. I say “almost” because there are two ways in which this story manifests itself in security.
Image Source: Sketchplanations
Our individual backgrounds define how we see security
There are many things about cybersecurity I find fascinating, but one of the biggest is that, as an industry, we can’t agree on what security is, how to do it well, or even what matters most. I’ve realized that this isn’t random, and everything comes down to where people come from. How someone sees security is largely defined by the roles they’ve held, the kinds of companies they’ve worked in, and what they’ve been responsible for.
A big reason for this, I think, is that very few people actually go to school to study security in a formal way. That’s very different from other fields, where everyone spends a few years building the same foundation at school before starting to work. Sure, people pivot careers everywhere, but most accountants study accounting, most biologists study biology, and so on (I haven’t checked the data, so take this as anecdotal, but it generally holds up). In security, there isn’t much of a shared baseline. People come in from all walks of life, learn on the job, and only later pick up more standardized knowledge through certifications or experience. That’s what makes our industry so diverse, but also why perspectives we hear can vary so much from one person to another.
While everyone’s experience is definitely unique, I think you can often tell how someone thinks about security just by understanding their background. It’s not a perfect rule (people are more complex than that), but I think I can say that more often than not, these generalizations are at least somewhat true.
Six examples of how our backgrounds inform how we see security
Security leaders with a background in software and security engineering
Security professionals and leaders with a background in software engineering tend to see cybersecurity as a technical problem that can be solved with better systems, better design and architecture, and more consistent processes.
Former engineers turned security leaders tend to see security as something you can build and improve through better systems. They think in terms of architecture, automation, and fixing problems at the source, which is why their teams are often more engineering-driven. They are more likely to build their own detections, create internal tools, and design systems that are secure by default. In tech companies, especially, where customers often ask how their data is protected, CISOs sit closer to revenue than in most other industries, which is why when you hear someone talk about security as a competitive advantage, they’re often coming from tech background. Not surprisingly, many companies in the Bay Area, and tech companies more broadly, hire heavily from this pool of candidates.
Security leaders with a background in IT
Security professionals and leaders with a background in IT and infrastructure security often come from much more complex environments than their software engineering peers, where security is a part of keeping the business running. They know that not every company is a software company, and that sometimes you have to secure what you have because you don’t have the luxury of rebuilding the entire infrastructure from scratch. They focus on managing systems, controlling access, patching vulnerabilities, minimizing downtime, and designing processes that enforce consistency at a large scale. This may sound less exciting than building new tools, but it’s exactly what their companies need to stay secure. When you’re dealing with 5,000 to 50,000 employees across different states or countries, each with its own constraints, security becomes less about having a flashy solution and more about maintaining visibility, control, and reliability across a very large and complex environment.
Security leaders with a background in law enforcement
Security professionals and leaders with a background in law enforcement often approach cybersecurity through the lens of investigation and accountability. They are used to thinking in terms of cases, i.e., what happened, who was involved, and how to put together a clear story from incomplete information. This often (but as I’ve said, not always) influences how they build security programs, with a strong emphasis on visibility, detection, and understanding events after the fact, not just preventing them upfront. They tend to be especially strong in areas like incident response, forensics, and insider threat detection. There’s a good number of ex-FBI and ex-police security leaders, and from what I’ve seen, they are very strong when it comes to bringing structure and rigor to investigations, asking the right questions, and making the organization truly understand and learn from security incidents.
Security leaders with a military background
Security professionals and leaders with a military background often think of security as a matter of defense strategy, planning, and execution. They focus on protecting critical assets, preparing for different attack scenarios, and making sure the organization can respond in a structured and coordinated way. There is a large number of ex-military CISOs, and if there’s one thing I’ve seen many of them have in common, it’s their ability to invest heavily in preparation before something goes wrong, and always having a solid plan in place. CISOs who are ex-service members are especially strong at building disciplined programs with clear roles, defined processes, and strong communication. I’ve seen several times that when incidents happen, they are the best to bring structure and make sure everyone knows what to do and how to move forward without chaos.
Security leaders with strong experience in compliance
Security professionals and leaders with a compliance background tend to think in terms of building comprehensive risk management programs, aligned with frameworks relevant to their organization. They like to make sure that at any time, the organization can show that it is doing the right things, has the right controls, and that all of the security efforts map to some objective requirements. I’ve noticed that CISOs who spent some time in GRC are especially strong at building documented, repeatable, and defensible programs.
Security leaders with experience in law
Even though there aren’t as many lawyers pivoting careers in security, I have met a few. Based on what I’ve seen, they tend to look at cybersecurity through the lens of risk, responsibility, and consequences. The people I’ve talked to seem to focus a lot on liability and making sure the organization is protected when things go wrong, and care a lot about liability exposure, contractual obligations, and minimizing legal and financial risk.
Each of them is right, and they are all wrong
There is most definitely an infinite number of ways we can categorize people’s backgrounds. Some start in a security operations center, others as auditors, and some, such as George Kurtz, founder & CEO of CrowdStrike, as Certified Public Accountants. The examples I mention here are just the ones that come to mind as I am thinking about people I’ve met, but they are in no way exhaustive. I have, for example, met a former HR who became a CISO (such a fascinating journey!).
The most important part is that, depending on people’s backgrounds, they see cybersecurity differently. Ask a former engineer, and they’ll talk about systems, architecture, and how things break; ask someone from compliance, and they’ll focus on controls, frameworks, and audit readiness; ask someone with a military or intelligence background, and they’ll think in terms of adversaries, detection, and response under pressure. Each person in security comes with a completely different mental model. So who’s right? They are all right, and they are all wrong at the same time. Like in that old story about the blind people and the elephant, each perspective is important, but none of them sees the whole picture.
There’s no single right way to secure a company, because there’s no single definition of what needs to be secured
The second dimension we need to keep in mind is that every company has different security needs. The way you would secure a B2B SaaS platform is very different from the way you would secure a bank with 1,500 branches all over the U.S., which, in turn, is very different from how you’d secure an international cruise line, or a firm that manufactures dental implants, or a hospital… When you pause for a moment and think about it, I am sure it will make sense, but way too often we as an industry conveniently forget about this reality. There’s no single right way to secure a company, because there’s no single definition of what needs to be secured. Every industry comes with different infrastructure, every company is at a different stage of maturity, and everything considered, you truly need to understand where they are to suggest that they need to do something. Which brings us exactly where we started - that Blind Men and the Elephant is the story of cybersecurity.
It’s a mistake to believe that any one view about security is enough, or that any one approach is the right way to secure every company. Real security comes from understanding the system, the business, the risks, and the tradeoffs as a whole, and figuring out what is appropriate for this specific environment at this specific stage, with these specific constraints, etc. It’s all these nuances that make specific controls very effective or utterly useless.
In the end, cybersecurity is about seeing enough of the elephant to make the right decisions, and making sure you focus on your own elephant, and not on the stories about elephants you’ve been hearing from others.
For founders, all this means that they really need to understand what problems they are solving and for whom, before approaching CISOs. More importantly, we as an industry should really keep in mind that panels and talks about “how everyone should do security” are pretty unhelpful. I am hoping that we will see more panels with diverse perspectives - diverse in terms of the kinds of businesses people are securing. When you have a panel of 4 SaaS CISOs, you won’t get as much of a different perspective as when the 4 people on the panel come from very different environments (one from SaaS, one from regulated industry, one from OT-heavy environments, and so on).


Security leaders from an economics and psychology background is perhaps what is missing here...
@ross, great article. Perspectives is what keeps us sane in this game called life and is very important in corporate
situations and it comes across in so many different ways.